Pre-holiday warning: Hackers want more than your data – they crave your cash! People who have worked hard for years to become successful – you or people you know – will have their lives ruined by cybercriminals this holiday season. Life savings and businesses’ capital will be stolen online, turning twelve drummers drumming and eleven pipers piping into twelve hackers hacking and eleven thieves a-thieving.
It’s the season of sharing but thieves want to take that “sharing” way too far. There are cyberterrorists that hope you are so excited about taking time off for Christmas that you’ll let your guard down.
The 12 days from Thursday, December 22, through Monday, January 2, present the greatest opportunity for cyberterrorists throughout the United States and across the globe.
Instead of ten lords a-leaping, you could be seeing ten cyberterrorists terrorizing. Instead of nine ladies dancing, you could be experiencing nine ransoms paying.
These are the days when many of your employees – including your IT team that is keeping your data secure – are taking time off. They are leaving your company’s data – including all your financial data, access to your bank accounts, customer lists and trade secrets – vulnerable to be stolen.
Instead of eight maids a-milking, you could be experiencing eight bank accounts a-busted.
Recent media reports detailed that over 100 hospitals were hit by a ransomware attack that collected the private data of patients and employees. Such an attack also could compromise a hospital medical team’s ability to perform surgeries.
Instead of seven swans a-swimming, you could have seven scammers scamming.
Now that mid-sized and larger companies are paying greater attention, you are the lowest-hanging fruit – you as an individual and the small company that you own or work for.
You may be too small to have a skilled IT professional, so you have assigned the position to good old Jerry because he’s “good with computers.” Jerry may never have taken a cybersecurity training course, but you have him virtually for free – maybe just an extra $100 per month.
You are risking your entire future and every dollar that you have earned by failing to be diligent in protecting your IT. On the 12 days that hackers call their World Series/Super Bowl/March Madness, you are leaving your company completely exposed with a welcome mat inviting an intrusion.
Instead of six geese a-laying, you are likely to have six criminals grabbing my crypto.
And don’t even consider the security of the cryptocurrency that you have saved for your retirement or for a company expansion. If your investment didn’t decline or go away in the FTX debacle, you could lose it all to a hacker across the world.
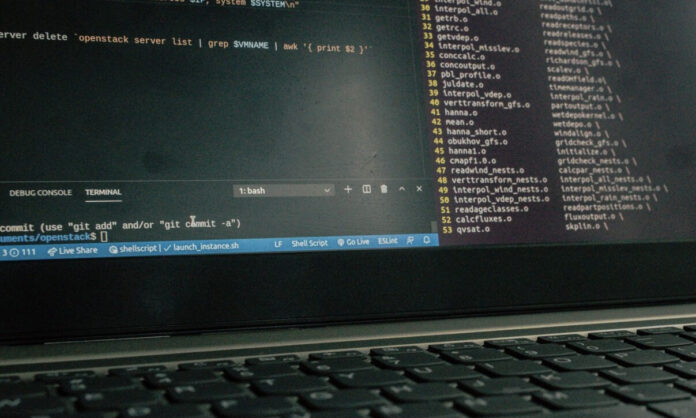
That brings up another point. No longer are the hackers 18-year-old high school dropouts drinking Yoo-Hoo and energy drinks while wearing a hoodie in their parents’ basement. Today’s most prolific hackers are actual businesspeople who invest their resources in emerging technologies that leave your company vulnerable.
Instead of five gold rings, you experience five empty bank accounts.
This generation of hackers can send a single clickbait message to millions of computers simultaneously.
Where the money goes will astound you: Cyberterrorism supports human trafficking, drug smuggling, and other nefarious activities.
Four calling birds can become four failing friends if they lose access to their cash.
What are the steps you can take to protect yourself?
- Know your risk. Admitting that you have a problem and seeking help will help win the battle.
- Implement systems to protect yourself such as security awareness training. This includes two-factor authentication on everything (and no password of abc123).
- Don’t let your guard down because hackers don’t take holidays off. Holidays are their busiest and most fruitful time.
- FBI cybersecurity expert Brett Leatherman emphasizes that we should use passphrases instead of passwords. Instead of Romeo123!, use a phrase you will always remember and have the final word reference the site, such as: My cat Fluffy l0ves Amazon! Or MycatFluffyl0vesAmazon!
Three French hens could become three sad shoppers.
Please notice in the two examples above that one version has spaces. Here’s a comparison according to Passwordmonster.com:
- Romeo123! Would take 1.3 seconds to crack
- MycatFluffyl0vesAmazon! Would take one thousand years to crack
- My cat Fluffy l0ves Amazon! Would take 82 billion years to crack (not all programs allow spaces, and some companies such as AT&T do not allow you to use their name, so you create a generic word such as ‘call’ for AT&T: My cat Fluffy l0ves Call!
Two turtledoves could become two folks with no gifts.
Finally, instead of And a partridge in a pear tree could be And it all could have been avoided!
You can protect your life savings and your company’s cash from cyberterrorists by calling a trusted local IT company. Taking action today can make your Christmas very merry instead of very scary!
We wish you a Merry and safe Christmas.
Michael D. Moore is founder and CEO of M3 Networks in Southlake.